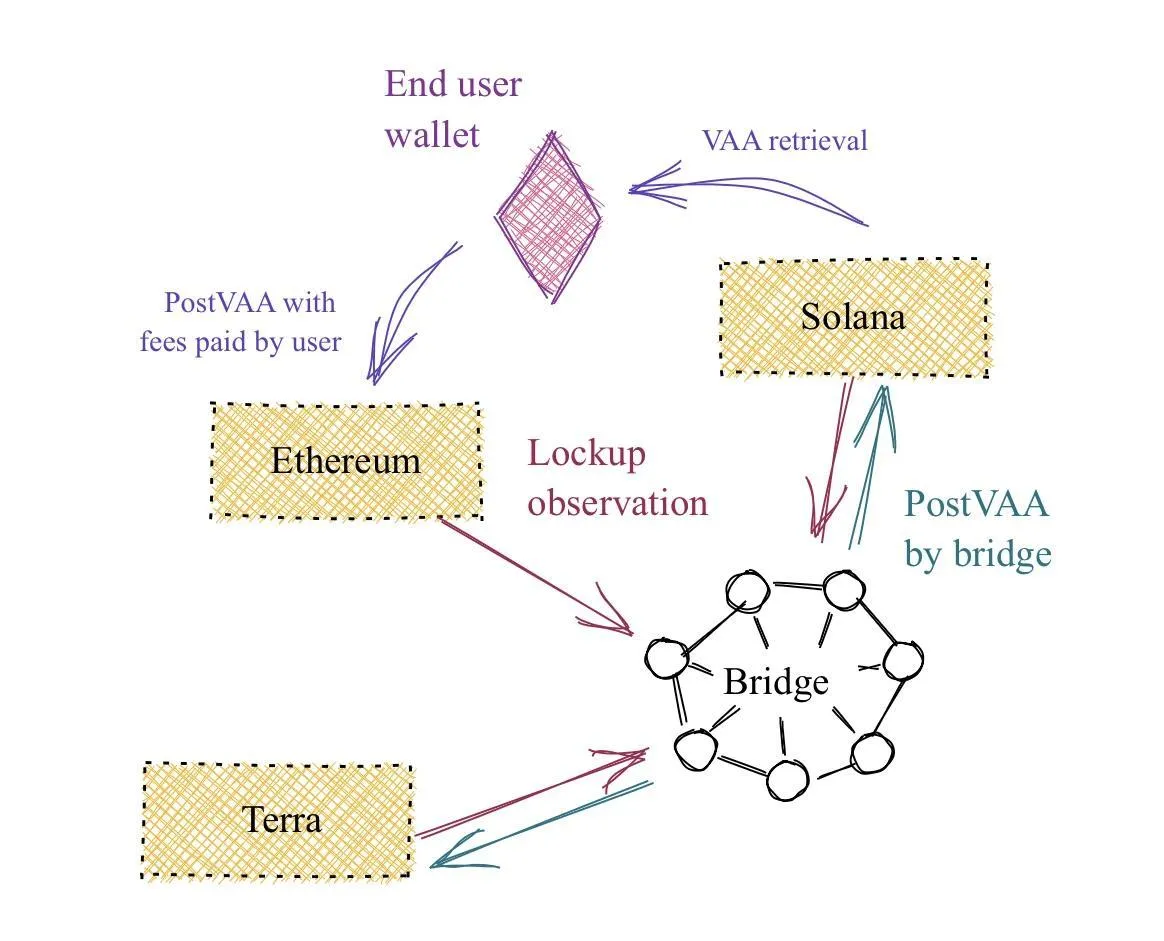
The implementation of crypto bridges has now become an important part of blockchain infrastructure, driven by increased activity across various networks. Since platforms such as Ethereum and Solana operate independently, users require mechanisms to transfer funds between chains without relying on central exchanges.
Source: Everstake
Cryptobridges enable cross-chain transfers of tokens, data, and digital assets without requiring custody.
This means that crypto bridges help connect dapps across different ecosystems so users can engage with multiple chains at once. Crypto bridges enable cross-chain transactions, so users do not have to convert assets to access different networks.
The Crypto Bridge working mechanism
Cryptocurrency bridges are designed to maintain the consistency of assets across different blockchains. They can be based on either a lock-and-mint or a burn-and-release mechanism.
In lock-and-mint technology, assets are locked in a smart contract deployed on the source blockchain. In turn, these assets are locked by the bridge, and their counterparts appear on the destination blockchain. Such tokens, called wrapped assets, can be used to interact with decentralized applications in a new blockchain environment.
The burn-and-release mechanism works in the opposite direction; it involves burning a wrapped token on the destination blockchain, which unlocks the initial asset and returns it to the source blockchain. It should be noted that the amount of assets does not differ between the two blockchains.
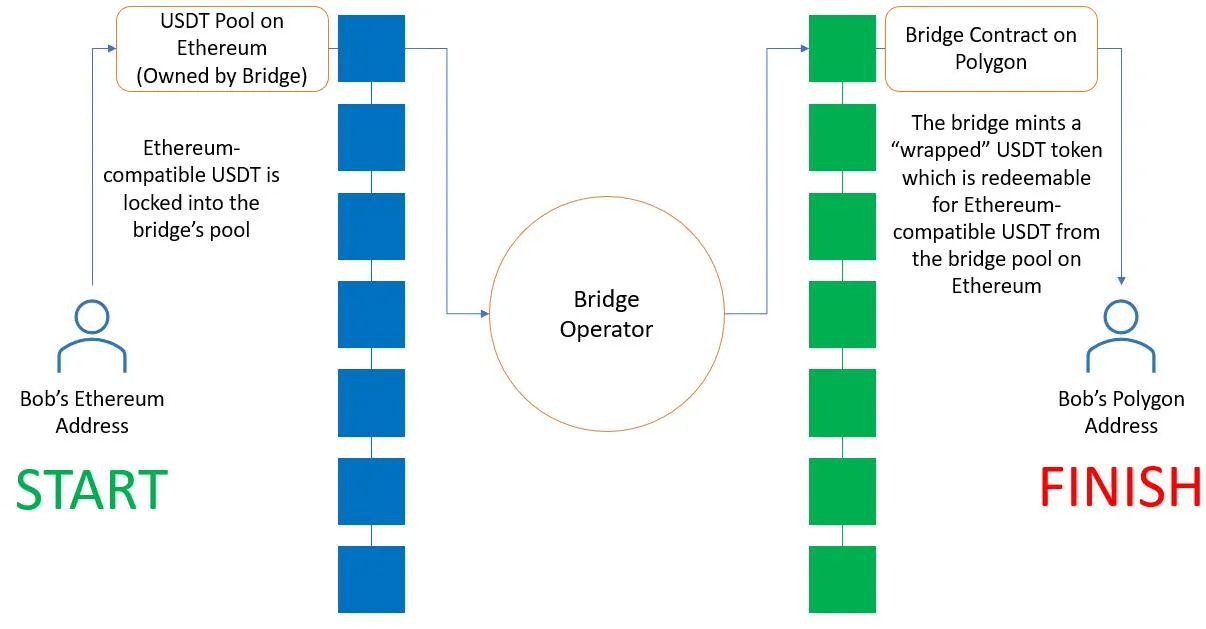
Source: medium
Additionally, some crypto bridges make use of validators, relayers, oracles. These elements verify transfers before the issuance or release of assets under the bridge design.
Categories of Crypto Bridges.
Crypto bridges can be divided into two categories based on their operational structure and trust assumptions.
Reliable bridges are based on centralized bodies that control the custody in transfers. Such systems can handle transactions at a fast rate but require only one operator.
Trustless bridges are decentralized (built on smart contracts and validation systems) and do not rely on any trusted authority. These designs do not rely on centralized control and are consistent with the infrastructure of decentralized finance.
Native bridges are embedded in blockchain ecosystems to enable direct transfers. One such project is the Arbitrum Bridge, which connects Ethereum to its Layer 2 network.
Significant Crypto Bridges are being used.
Several protocols are extensively utilized owing to their design and network support.
In Protocol, relayers are used to achieve transfers to minimize waiting time. Wormhole is a system that links over 30 blockchains and supports token and NFT transfers. Stargate deploys a single liquidity model, which can transfer without fragmented pools. Synapse Protocol uses token swaps and bridging in a single transaction.
Circle Cross-Chain Transfer Protocol implements a burn-and-mint approach to transfer USDC across chains, without wrapped assets. deBridge concentrates on cross-chain messaging and enhanced data transmission.
The significance of Crypto Bridges in the operation of the Blockchain.
Crypto bridges are providers of decentralized apps on different networks. This allows users to move assets between environments with different transaction costs and processing speeds. To illustrate, Ethereum users can migrate their assets to other networks to pay lower fees or access a specific application.
Crypto bridges also facilitate liquidity allocation, enabling assets to be located across different ecosystems.
The position can be used in decentralized finance, where liquidity availability can affect trading volume and capital allocation. Also, bridges help alleviate congestion in high-contention networks by allowing users to shift activity across chains.
Security Risks in Crypto Bridges
Crypto bridges are vulnerable to exploits because they handle and move assets. Smart contract, validator system, or key management vulnerabilities have resulted in major losses in previous attacks.
The Ronin Bridge and Poly Network cases illustrated that the vulnerability of bridge design can be exploited. These incidents point to vulnerabilities in the validator control and contract logic.
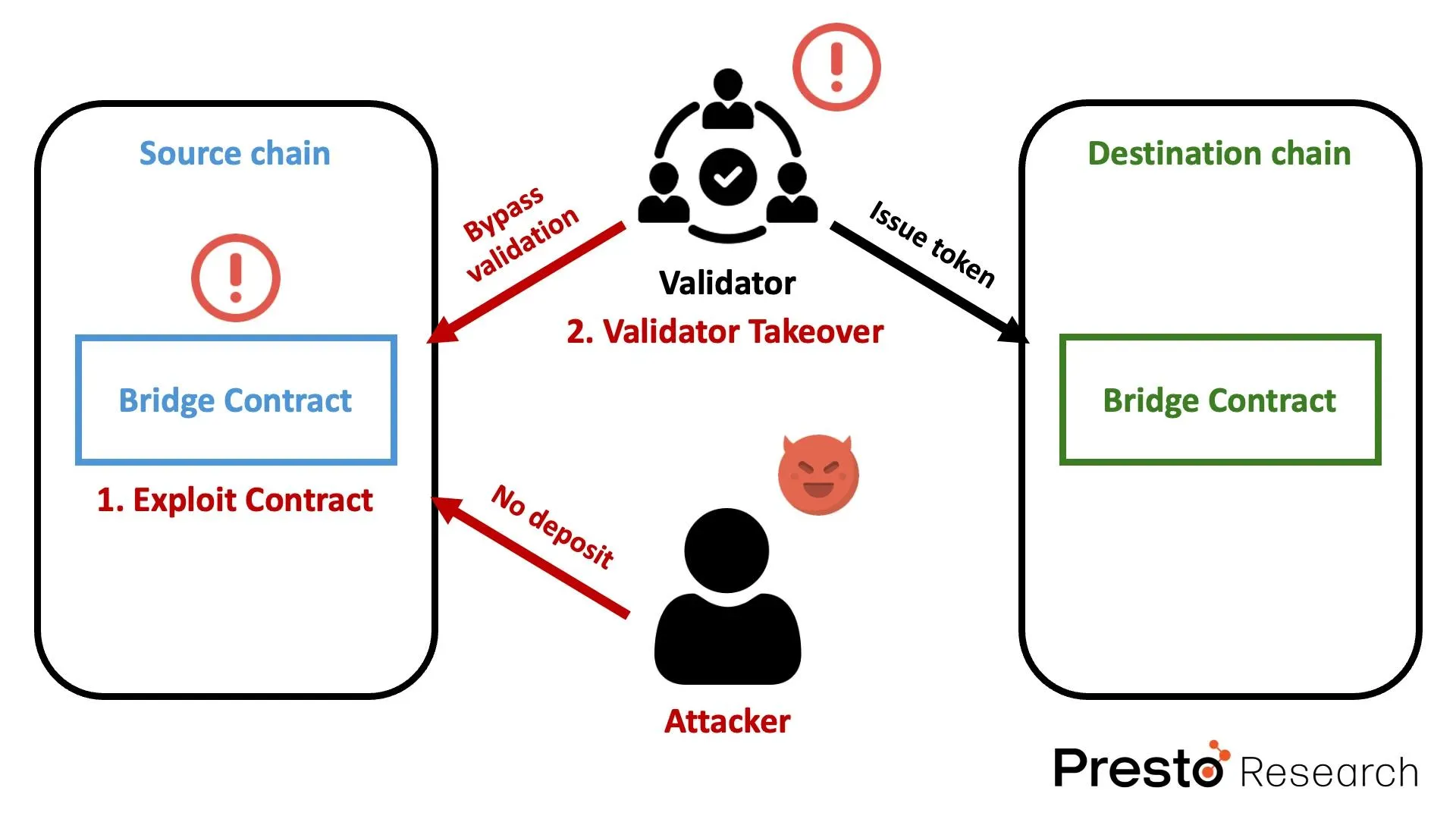
Source: prestollabs
In an attempt to reduce exposure, users are likely to adhere to protocols with a documented audit track record and transparent operations. Validating official interfaces nd verifying transactions are typical activities when utilizing crypto bridges.
What Users need to consider.
Before using crypto bridges:
- Check the audit history and development activity of the bridge.
- Visit only official websites to protect yourself from phishing scams.
- Do smaller deals before bigger ones.
- Knowledge: Learn whether the bridge you plan to use is centralized or decentralized for validation.
- Keep track of transaction costs.
Conclusion
The fact is, crypto bridges remain an important component of blockchain technology, enabling cross-chain communication across separate blockchains. They ensure the coherence of the asset transfer process by using lock, mint, burn, and release methods.
FAQ
What are crypto bridges used for?
Crypto bridges: bridges that allow the exchange of information and assets across multiple blockchain networks.
Are crypto bridges based on wrapped tokens?
There are also so-called burn-and-mint schemes, and some bridges use so-called wrapped tokens using lock-and-mint models.
Do crypto bridges work?
Security is determined by the bridge design, audits and validator structure.