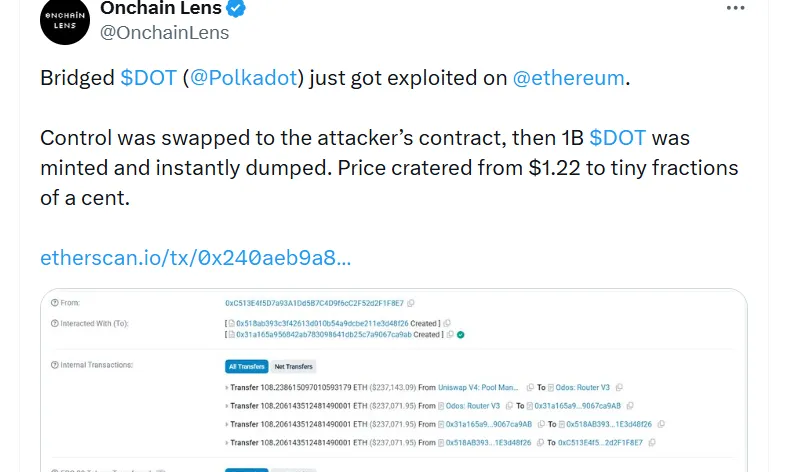
Key Insights:
- The attackers were able to mint 1 billion fake tokens through Polkadot bridge exploit with low liquidity, making the attack only profitable to the tune of 237K.
- In the global scene, cross-chain bridge vulnerabilities have contributed a greater percentage of 60% to overall crypto hack losses.
- The largest vulnerabilities in bridge infrastructure are weak validation logic and flaws in the administration controls.
Following an attack on a cross-chain bridge connected to Ethereum, Polkadot found itself in the middle of a big adventure. The attack gave the opportunity to mint almost 1 billion DOT tokens with bridges in several minutes. The attacker soon resold the newly generated supply through decentralized exchanges, earning him around 108.2 ETH, which was worth around $237,000.
The damage was contained to a great extent, given the shallow liquidity conditions, even though the mint was massive. The price of the bridged token plummeted to fractions of a cent nearly immediately after being around $1.22. Notably, the Polkadot native relay chain was not compromised and it was not affected by the incident.

Hackers use gateway validation weakness mechanism.
The attack was based on a bug in the Ethereum gateway contract validation logic at Hyperbridge. Attackers provided a forged cross-chain message, which evaded important verification in the system. This message was accepted as valid and it was passed on to the token gateway contract.
After being accepted, the malicious instruction implemented an administrative change of the bridged token contract. This practically gave the full minting control to the address of the attacker without the activation of safeguards. The attacker minted the whole 1 billion tokens supply in one transaction with admin privileges obtained.
Bridge vulnerability does not impact polkadot ecosystem.
The protocol or consensus level compromise of Polkadot was not directly affected during the exploit. The issue was only in the Ethereum-side infrastructure that dealt with representations of bridged tokens. Consequently, indigenous DOT provisioning and on-chain business were not impacted.
Nevertheless, the event caused precautionary measures in the wider ecosystem and the interactions. Exchanges like the Upbit and Bithumb have temporarily shut down DOT deposits and withdrawals to prevent misunderstanding. On the one hand, Polkadot experienced only moderate increases and decreases, however, the overall mood towards cross-chain security was short-lived.
Cash shortage cripples dump profits.
The dynamic of liquidity was critical in curtailing the financial benefit of the exploit by the attacker. The DOT liquidity pools based on Ethereum did not have deep enough liquidity to handle the huge influx of tokens. Consequently, the attacker experienced extreme slippage when it came to executing the sell-offs transactions.
In spite of the 1 billion tokens to be minted, the value achieved was pegged at about $237,000. On-chain data of various analytics companies proved that the tokens were directed to DEX aggregators towards DOT-ETH pools. What would have been a far greater loss in deeper markets would have been the same exploit.
Increasing bridge exploits highlight the continuing security threats.
This attack is part of an increasing trend of cross-chain bridge attacks that have been witnessed in 2026. The previous incidents are the $4.3 million exploit of itube and a breach of $25 million with Resolv Labs. These attacks are commonly based on the administrative controls or validation of bridge infrastructure.
Bridge failures have emerged as the largest portion of all crypto hack losses, with a figure of more than 60% according to blockchain analytics data. Such exploits have already cost the industry more than $2 billion in cumulative damages. The incident involving Polkadot supports the continued consideration of the message verification and central control points in bridging systems.
Security firms, such as PeckShield and CertiK, noted that the exploit used was a well-known infinity mint attack. The low validation enabled the attackers to create authenticity and take control of the token issuing systems. With the growing interoperability across chains, it is a top priority among developers and auditors to secure these systems.