The science of cryptography comprises the encoding of information. Cryptography emphasizes the need to ensure secure communication and data privacy.
There are two techniques used for doing so:
- Private Key (Symmetric Key Cryptography)
- Public Key (Asymmetric Key Cryptography)
Even though both techniques are employed to secure information, they operate in different ways and possess some strengths and weaknesses.
This article will concentrate on highlighting the main features of the private and public keys, along with their pros and cons.
What Are Private Key and Public Key?
A private key, also known as a symmetric key, is an encryption technique involving the use of two related yet distinct keys: one is used publicly for encrypting data, while the other is used privately for decrypting it or signing digital documents.
Source: Medium
A public key, also known as an asymmetric key, is a secret key that is utilized for decrypting data that is encrypted using its corresponding public key or for producing digital signatures.
The private key makes sure that no one except the owner can access any confidential information. There is also no need for a shared secret between the two parties, as in symmetric cryptography.
The public key is intended for open distribution, while the private key is retained by its owner and not shared.
Private Key and Public Key in Cryptography
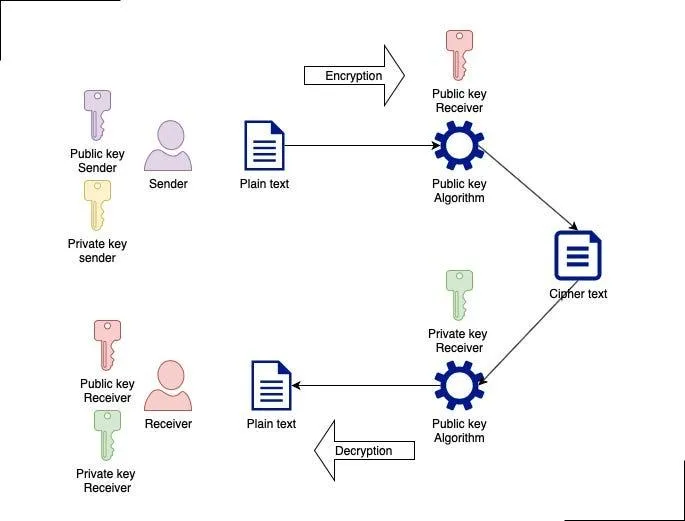
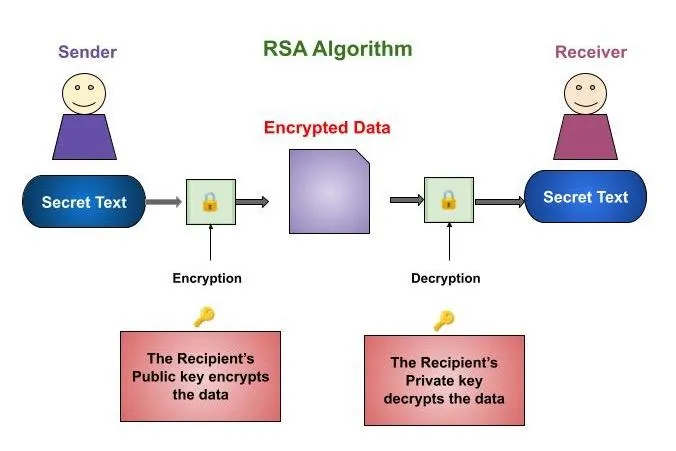
Both the private key and Public Key belong to an asymmetric cryptography mechanism where encryption and decryption are separate.
Encryption:
- The user encrypts data using the public key.
Decryption:
- The receiver decrypts the ciphertext with the use of the private key.
As the private key would not be transmitted, it is unlikely that there would be an interception. This encryption and decryption approach proves to be helpful when exchanging data through networks such as the Internet.
Private Key and Public Key
The link between Private Key and Public Key depends on the computation performed in algorithms such as RSA and elliptic curve cryptography, wherein Public Key is easily derivable, but deriving the Private Key from Public Key is not possible.
The use of the key pair in other uses is shown by the digital signature, where the private key creates a digital signature for a specific data collection.
Source: Tutorials point
This is because only the private key can generate such a signature, and it would therefore be impossible for anyone else to replicate it. The public key enables verification of this signature to ascertain that the information has not tampered with.
Impact on Digital Security System
The Private Key and Public Key have numerous applications across digital technology. They are used not only to ensure secure web connections but also to encrypt communication channels and build blockchain systems.
Short-term impact:
- Provides safe communication channels over unsecured networks
- Prevents any kind of data breach
Long-term impact:
- Allows establishing encryption standards
- Establishes trust within digital communication channels
In blockchain technology, the Private Key is used to authenticate and sign transactions, whereas the Public Key is used to create an address that can receive cryptocurrency.
What Users Need To Know about Private Key and Public Key
The handling of Private Key and Public Key involves distinct strategies based on their uses:
- Public keys can be freely distributed without any risk
- Private keys should always be kept secret
- A private key should not be disclosed under any circumstances
- Loss of a private key leads to loss of control
Private keys are typically held in protected environments, such as encryption software or hardware tokens. It is important that there are controls in place to prevent any other person from accessing them.
Related Topics
- Symmetric encryption methods and shared keys
- Hashing functions and integrity testing
- Secure data encryption protocols for communication
Frequently Asked Questions
How do a private key and public key differ from each other?
A public key is used for encryption or verification of data, whereas a private key is used for decryption and signing.
Can the public key give away the private key?
Is the private key information embedded in the public key?
No, because according to the algorithm, the private key cannot be found from the public key.
Where do we apply private keys and public keys?
They are applied in secure channels, digital signatures, and blockchains.
What would be the consequences of losing the private key?
There will no longer be any way to access data encrypted using the private key.
Conclusion
The idea of Private Key and Public Key is essential in asymmetric cryptography and makes secure messaging possible by virtue of its two parts. The design of such keys allows information that is encrypted using this technology to be freely exchanged but only accessed by the owner.